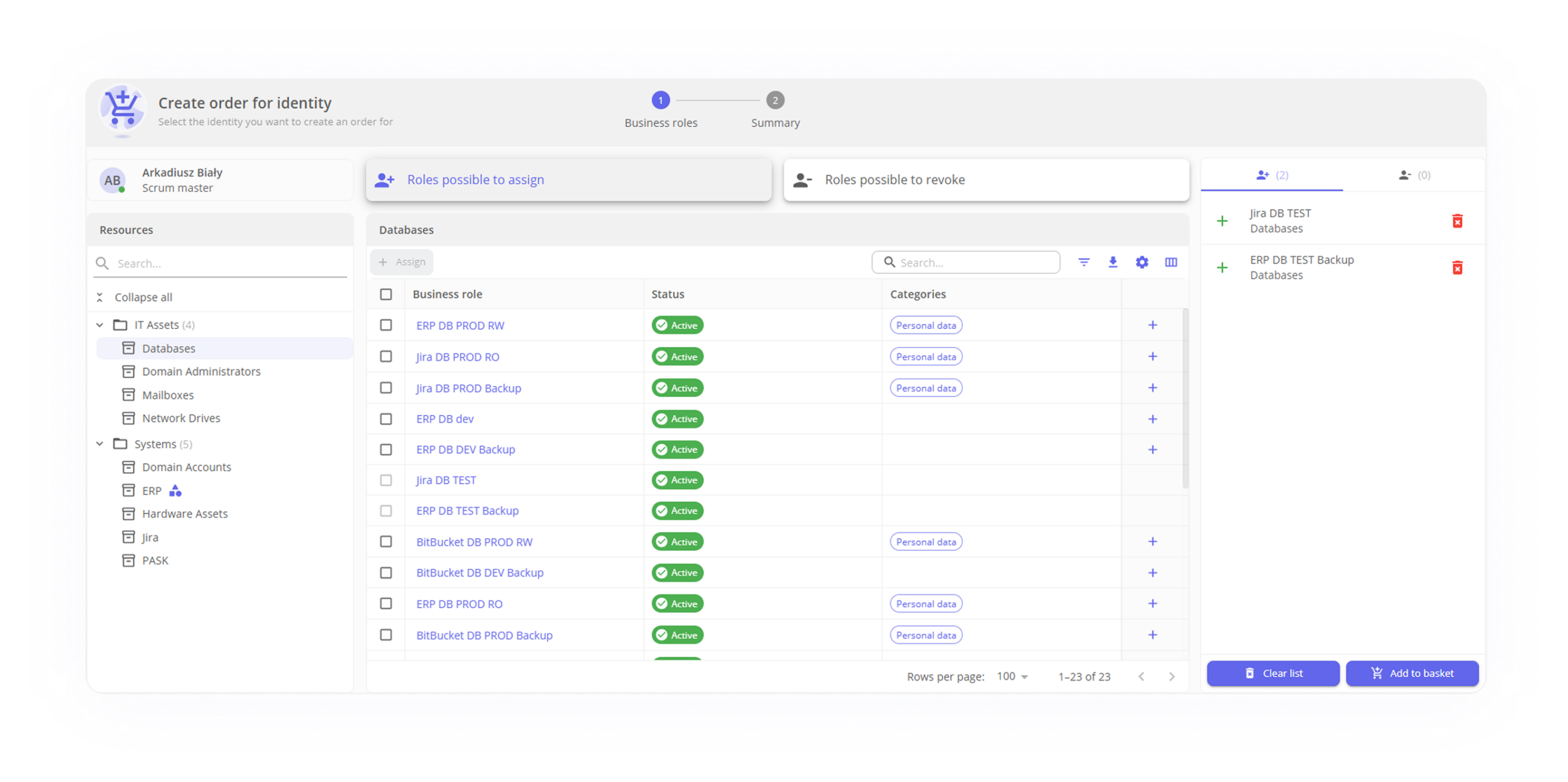
Access requests
Request to grant or revoke access for a single identity or group of identities.

Flexible request process
Automate, simplify, and customize every step of granting access, from approval to implementation. With PASK, you can create unique application scenarios—from simple, single-step paths for low-risk resources to complex, multi-step processes involving, for example, management or the security department.
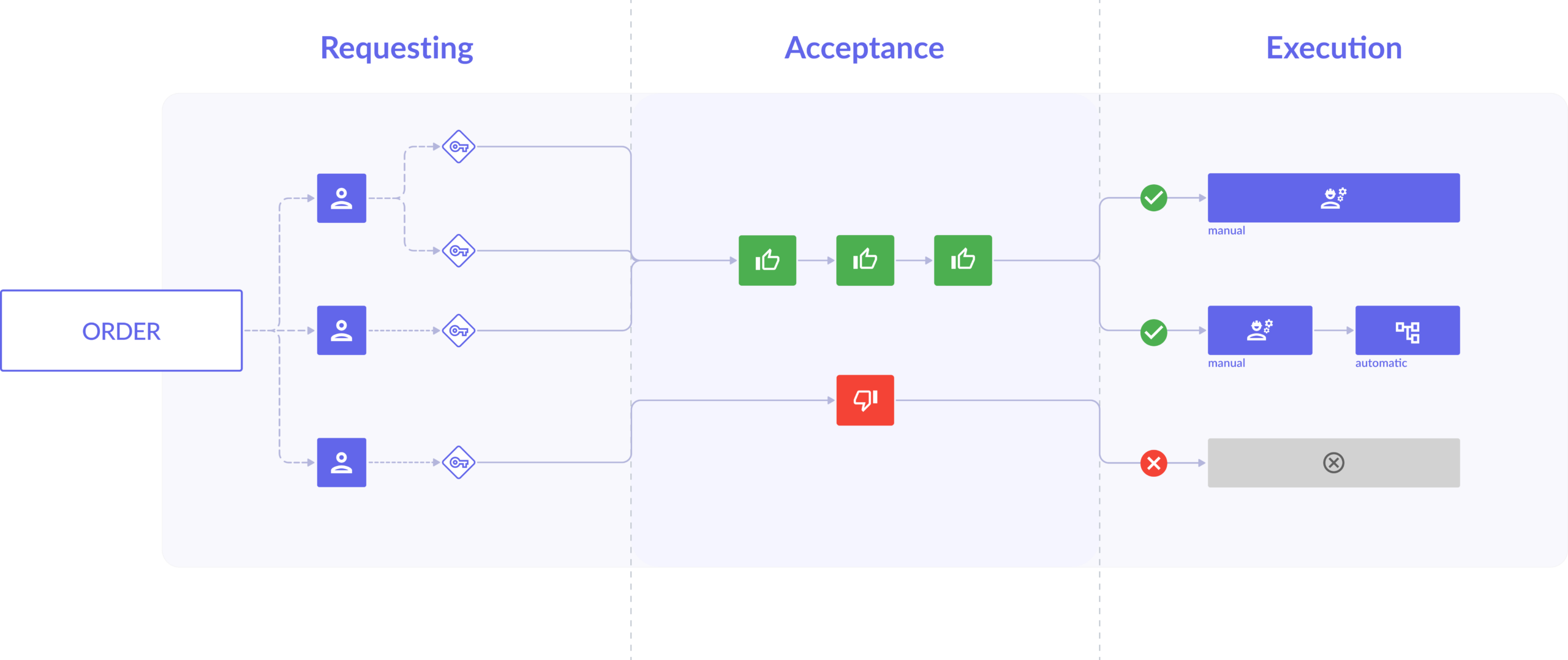
A tailor-made acceptance and implementation process
Configure application workflows to match your procedures. Create multi-step approval and fulfillment paths, require full compliance at key stages, and securely manage access limits. Once approved, the system will automatically assign permissions or delegate the task for manual processing.
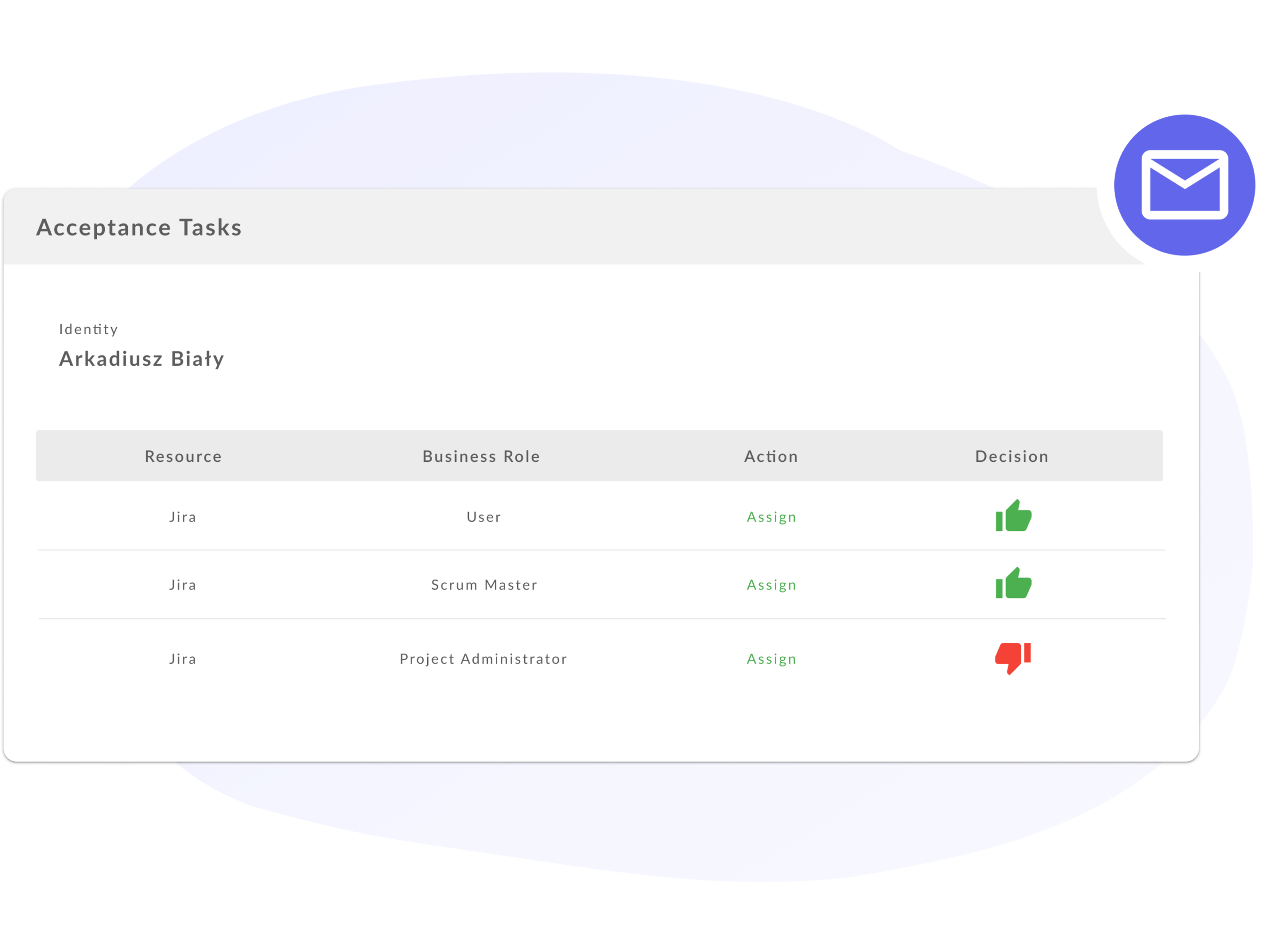
Acceptance by email
Make decisions with a single click, without logging in. Acceptors respond immediately via email, reducing application processing time and expediting access granting.
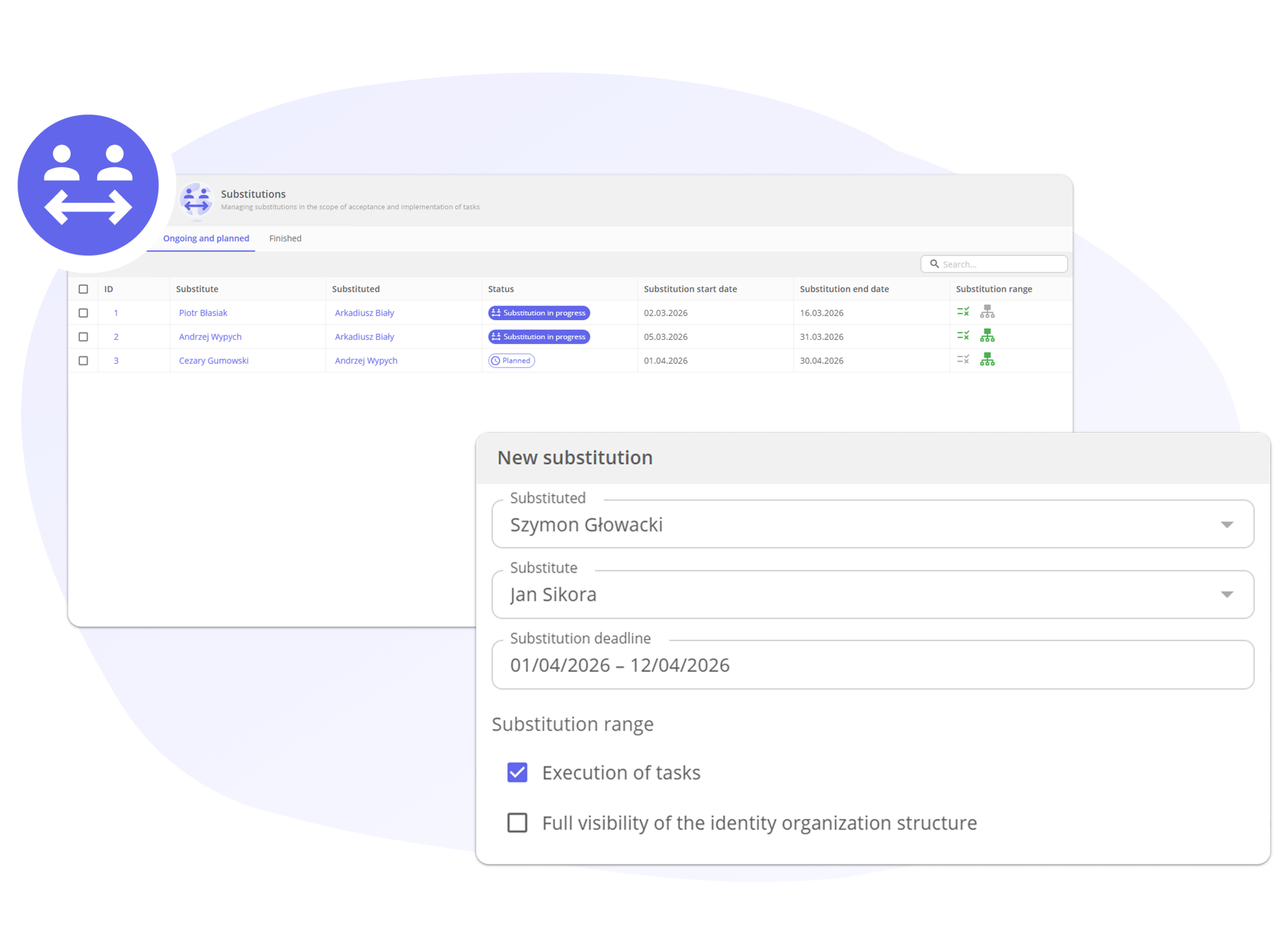
Substitutions
Maintain continuous approvals even in the absence of key individuals. Requests don't get stuck, decisions are made in a timely manner, and every approval is clearly recorded - with information about who made it, when, and why.
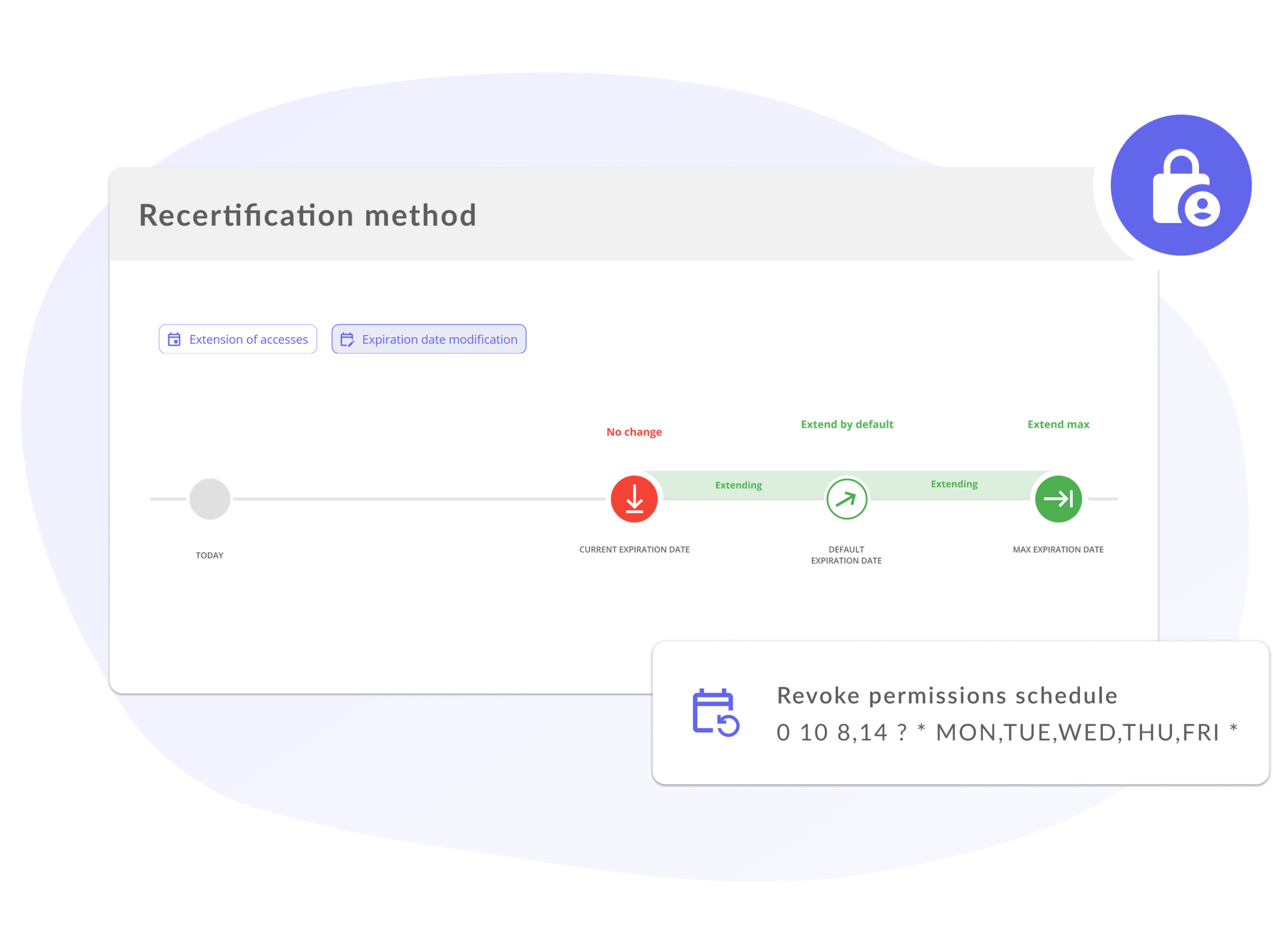
Automatic expiration of privileges
The system automatically monitors the timeliness of access requests and revokes them when they are no longer needed. It relieves users of manual control, supports effective offboarding, ensures compliance with security policies, and limits the number of redundant accesses.